Microsoft is introducing a new Exchange Online security feature that will automatically start throttling and eventually block all emails sent from “persistently vulnerable Exchange servers” 90 days after the admins are pinged to secure them.
As Redmond explains, these are Exchange servers in on-premises or hybrid environments that run end-of-life software or haven’t been patched against known security bugs.
“Any Exchange server that has reached the end of life (e.g., Exchange 2007, Exchange 2010, and soon, Exchange 2013), or remains unpatched for known vulnerabilities,” The Exchange Team explained.
“For example, Exchange 2016 and Exchange 2019 servers that are significantly behind on security updates are considered persistently vulnerable.”
Microsoft says this new Exchange Online “transport-based enforcement system” has three distinct functions: reporting, throttling, and blocking.
The new system’s primary goal is to help Exchange admins identify unpatched or unsupported on-prem Exchange servers, allowing them to upgrade or patch them before they become security risks.
However, it will also be able to throttle and eventually block emails from Exchange servers that haven’t been remediated before reaching Exchange Online mailboxes.
This new enforcement system will only affect servers running Exchange Server 2007 using OnPremises connectors to send mail to allow fine tuning before expanding to all Exchange versions, regardless of how they connect to Exchange Online, after tuning the
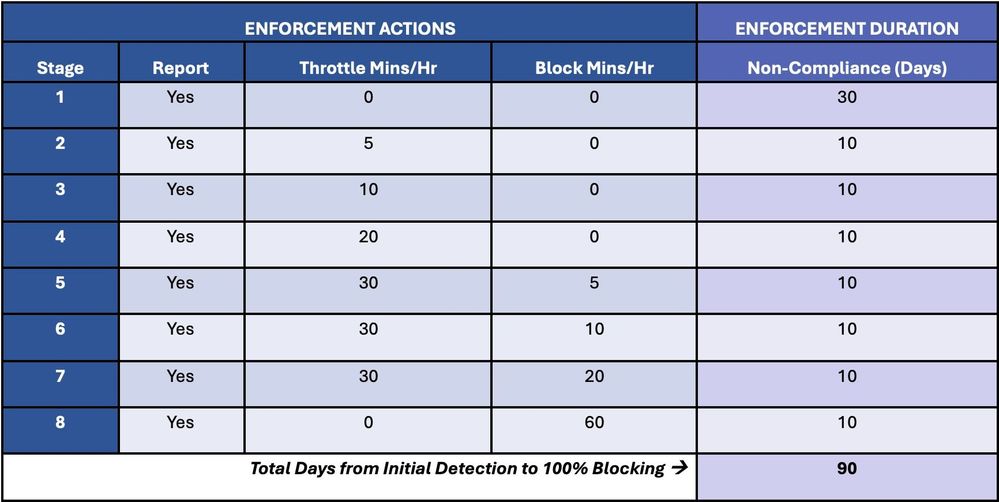
Redmond says it follows a progressive approach designed to gradually increase throttling and introduce email blocking until all emails sent from vulnerable servers are rejected.
These enforcement actions are designed to slowly escalate until the vulnerable Exchange servers are remediated by removal from service (for end-of-life versions) or patched (in the case of releases still under support).
”Our goal is to help customers secure their environment, wherever they choose to run Exchange,” said The Exchange Team.
“The enforcement system is designed to alert admins about security risks in their environment and to protect Exchange Online recipients from potentially malicious messages sent from persistently vulnerable Exchange servers.”
For some admins, ensuring that emails sent from vulnerable servers in their environment to Exchange Online mailboxes will not get automatically blocked will likely be another “incentive” that will add to their ongoing effort to keep end-users protected against potential attacks.
This announcement followed a January call to action when Microsoft urged customers to keep their on-prem Exchange servers up-to-date by applying the latest supported Cumulative Update (CU) always to have them ready for incoming emergency security updates.
Microsoft also asked admins to apply the latest patches on Exchange servers as soon as possible after issuing emergency out-of-band security updates to address ProxyLogon vulnerabilities exploited in attacks months before the official patches were released.
More recently, Microsoft patched another set of Exchange RCE bugs known as ProxyNotShell, two months after exploitation was first detected in the wild.
A Shodan search still shows a massive number of Internet-exposed Exchange servers, with thousands of them waiting to be secured against attacks targeting them with ProxyLogon and ProxyShell exploits, two of the most exploited vulnerabilities in 2021.